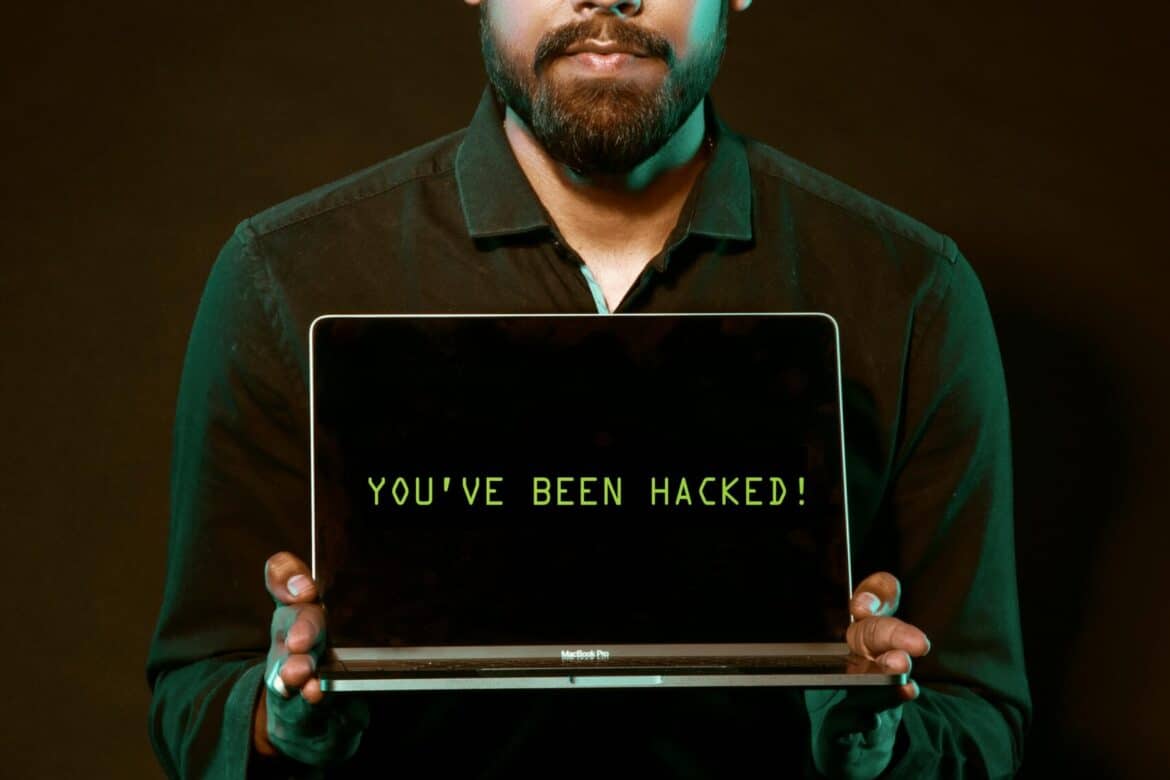
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off.
Welcome to the world of deepfakes. This is a rapidly evolving technology that … Read More